Introduction
We have previously discussed how Nucleon ensures robust endpoint security through continuous verification, least-privilege access, and AI-driven malware detection, all tailored to modern environments such as remote work and cloud systems.
We are now going to tackle Nucleon's key features, including its adaptive environment handling, real-time AI protection, and integration with Zero Trust architecture, to provide a comprehensive, flexible, and transparent security solution.
Adaptive Environment Handling
The absorption phase is crucial for the long-term effectiveness of nucleon’s EDR, serving as the initial step in formulating security policies tailored to that particular environment. This phase ensures that the EDR develops customized policies based on the regular usage patterns of the endpoint, rather than relying solely on generic rules like many other solutions.
The absorption mode is a unique learning phase that begins immediately after the agent is installed on a machine. During this period, the agent unobtrusively monitors all activities on the endpoint, without any interference. This learning phase is distinctive to Nucleon, as it prioritizes understanding the specific environment before implementing rigorous rules. By avoiding a one-size-fits-all approach, the Absorption phase guarantees that our policies align with the exact requirements of the environment, identifying threats without disrupting daily operations.
As previously noted, the agent actively monitors the user’s regular activities, including file access, network transactions, applications, and process behaviors. All these activities are logged, and the information is subsequently analyzed using machine learning algorithms to identify what constitutes normal behavior, enabling the system to detect any anomalies in the future.
The gathered data is analyzed by machine learning algorithms, which helps to formulate an initial Zero Trust policy with rules customized for your environment.
For example, if an application typically connects to a specific server, the system may establish a rule that permits only that particular connection. If your team’s behaviors evolve, such as the adoption of a new tool, the system can dynamically update these rules to ensure they remain relevant. The proposed policies are then reviewed by our MDR team to verify their accuracy before being activated to safeguard your endpoints. This adaptability allows Nucleon’s rules to evolve alongside your business, maintaining robust security without being excessively restrictive.
In contrast to Nucleon’s adaptive strategy, numerous traditional EDR solutions depend on pre-defined rules that remain unchanged with respect to your specific environment. These static systems operate using generic configurations or signature-based detection, which often fail to recognize emerging threats or mistakenly flag regular actions as suspicious, leading to interruptions.
Conversely, Nucleon’s Absorption Phase first learns your distinct patterns, establishing rules that align with your workflows. This makes our EDR more agile and precise, identifying genuine threats while allowing your team to operate uninterrupted.
This phase greatly decreases false positives by understanding the unique behavioral tendencies of an organization’s endpoints prior to enforcing Zero Trust policies. Throughout this initial observation phase, the agent passively tracks user activities, application usage, and network interactions, developing a personalized baseline of normal operations. By employing machine learning to create refined policies that accurately represent these legitimate workflows, Nucleon guarantees that standard actions are not erroneously flagged as threats, in contrast to traditional EDRs utilizing generic rules. This individualized strategy lessens disruptions, enabling organizations to sustain productivity while confidently protecting their endpoints from real threats.
The following image illustrates the primary differences between our EDR and conventional EDR solutions.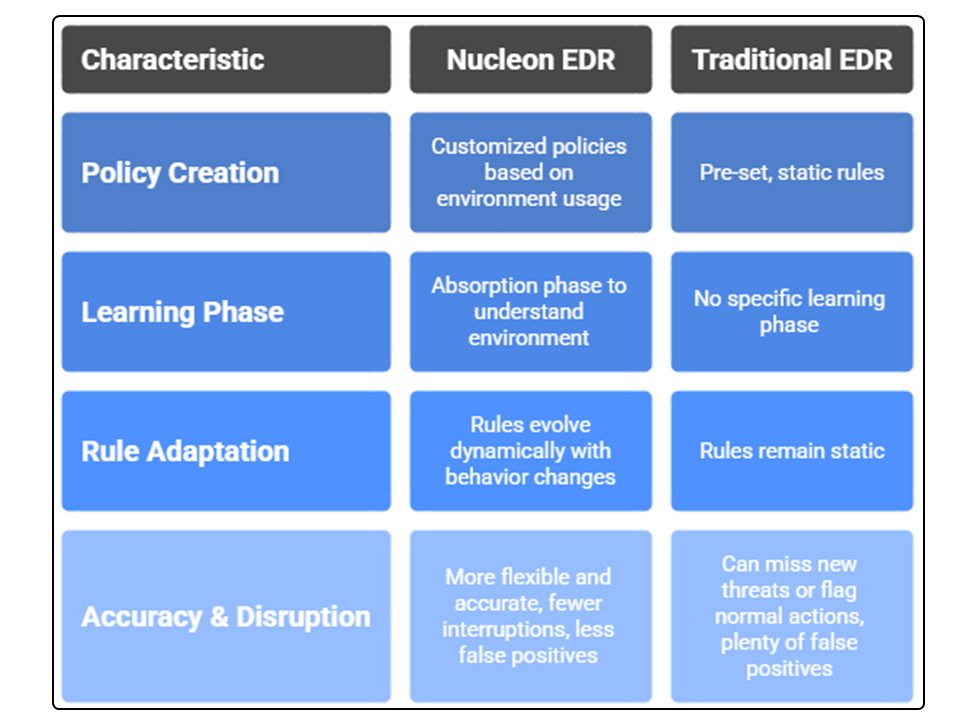
Real-Time AI Protection
Nucleon EDR Real-Time AI Protection establishes the foundation of its Zero Trust security model by utilizing cutting-edge artificial intelligence to oversee and safeguard endpoints in real time. In contrast to conventional tools that rely on predetermined rules or recognized threat signatures, our AI evaluates every file on the endpoint, detecting even the most elusive threats. This smart, flexible strategy ensures the security of your endpoints, regardless of whether your users are working remotely, using personal devices, or engaging in cloud applications.
The image below showcases how our AI engine makes sure that the endpoint is protected at any point of time, as we are going to explain each feature in detail later in the document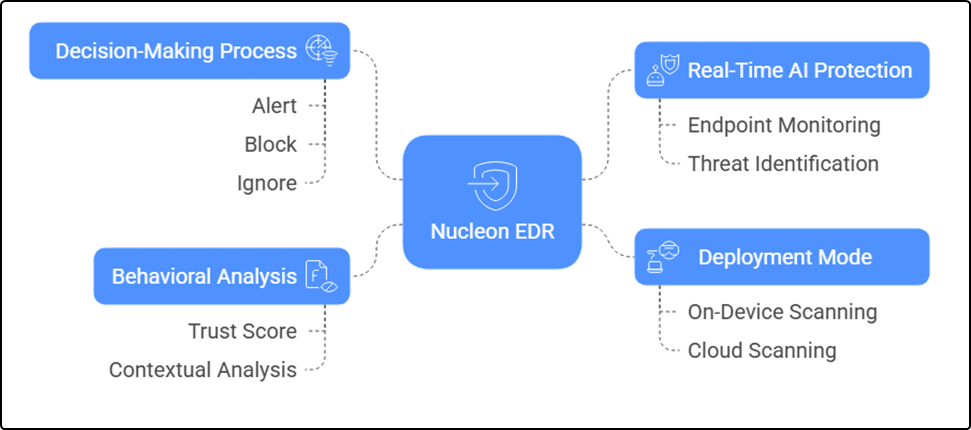
On-Device and Cloud AI for Real-Time File Scanning:
Nucleon's AI operates equally well on-device and in the cloud, continuously scanning each file in real-time. This method provides rapid and consistent protection for any endpoint where the agent is installed. For instance, when a file is downloaded, created, or altered on the endpoint, our AI scans it immediately to assess whether it poses a safety risk or is malicious before it can execute.
Such real-time enforcement is critical for detecting advanced attacks, such as zero-day exploits, which conventional systems might miss. By examining the file itself rather than merely comparing it to a set list of known threats, the AI can uncover malicious code and prevent the file from inflicting harm. This additional layer of security guarantees that even newly developed threats are identified swiftly. Nucleon’s EDR is crafted to facilitate this process smoothly, providing rapid, intelligent protection that secures your endpoints without hindering your productivity.
Our AI Goes Beyond Just Labeling Files; It Analyzes Their Structure
Standard security solutions, such as VirusTotal, frequently depend on file reputation, categorizing files as "safe" or "malicious" by utilizing hash-based scanning that matches files against a known threat database. This method faces challenges with unknown or modified threats, including zero-day attacks or malware that masquerades as legitimate applications.
Nucleon's AI is considerably more advanced. It performs a comprehensive scan of each file on an endpoint and assigns a trust score through an in-depth, real-time evaluation of its contents and structure. The agent reviews aspects such as the file type, coding patterns, and other features to allow our sophisticated AI model to ascertain if the file is harmful, benign, or uncertain. By scrutinizing the file's code for dubious characteristics, Nucleon's AI detects zero-day attacks and altered threats that conventional systems overlook.
Clear Decisions and Transparent Responses
Nucleon's AI not only makes judgments but also clarifies its reasoning, enabling you to comprehend the rationale behind how a file was treated. When the AI analyzes a file, it decides on the suitable action: alert (inform the team for further examination), block (isolate the file to avert damage), or disregard (if the file is harmless). For example, if the AI evaluates a recently downloaded executable and identifies its code as malicious, it can promptly block and isolate the file, generating an alert with specific details, such as "This file was blocked due to identification as a trojan." This transparency cultivates trust and allows you to monitor exactly what occurs on your endpoints. The AI leverages the file's trust score and risk level to determine an appropriate action, assisting your team in concentrating on genuine threats without being inundated with superfluous notifications.
Integration with Zero Trust Architecture
Nucleon EDR's Zero Trust framework is inherently integrated into its architecture, offering a structured approach to endpoint security through careful management of every procedure. The Zero Trust model does not assume any built-in security, necessitating continuous verification for all interactions. Nucleon EDR embodies this principle by tracking the endpoint to verify that all users, devices, applications, or processes adhere to stringent policies. This integration is intended to function effectively in dynamic settings, including remote work environments, the use of personal devices, and cloud infrastructures, delivering a robust defense that can adapt to continuously evolving threats.
The subsequent image illustrates the three key components of this integration, highlighting how Nucleon EDR ensures reliable and precise endpoint security, which will be detailed in the following paragraphs.
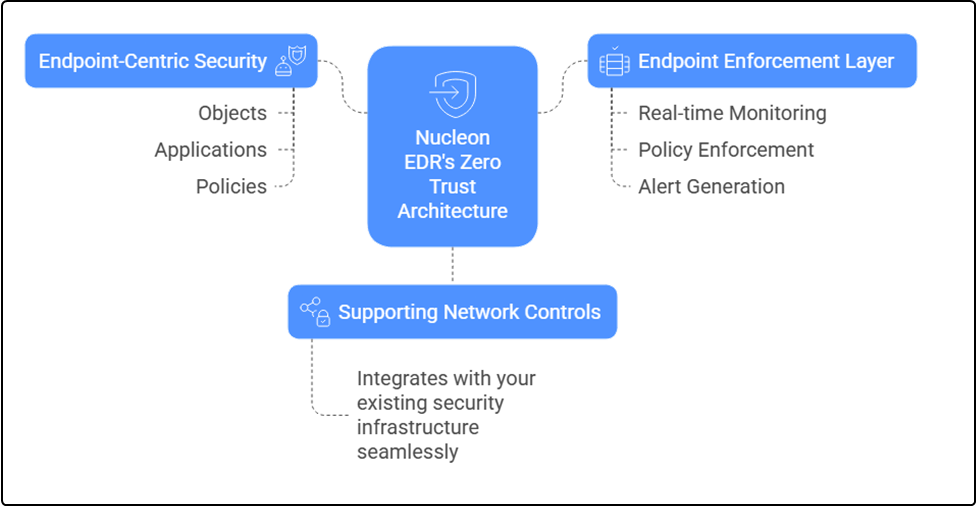
Endpoint-Centric Security with Policies and Rules
Nucleon EDR safeguards endpoints by implementing Zero Trust principles directly on the devices, closely regulating every action taken. The system is constructed from three core components: objects, applications, and policies. Objects represent distinct items, such as a specific command, process, or executable (like a PowerShell script or an .exe file). Applications bundle related objects together, for instance, all the elements of a program like Microsoft Word or OneDrive, simplifying rule management. Policies consist of a set of rules applied to devices or user groups, defining what actions are allowed and which are not.
As an illustration, it might allow the "PowerShell" application to run particular commands while preventing changes to critical system files, such as a .dll file located in C:\Windows\System32. Each object is managed separately, enabling detailed rules, such as allowing software to read certain file types but prohibiting write access to them. This level of granularity ensures that only authorized activities are permitted, customized to meet the organization's unique needs. In rapidly changing environments, this endpoint-centered approach to security guarantees consistent protection regardless of user context or device location. Nucleon EDR is crafted to implement this level of control efficiently, allowing organizations to sustain strong security while keeping operational processes smooth.
Supporting Network Controls
Nucleon EDR does not directly oversee network firewalls or Zero Trust Network Access (ZTNA) gateways, but it enhances the overall security of an organization by supporting these tools. Firewalls serve to manage both incoming and outgoing data flow, generally performing filtering based on IP addresses or domain names. Nucleon EDR adds to this by implementing detailed rules at the endpoint level, offering an extra layer of security that operates independently of network conditions. For instance, while a firewall may allow traffic to a trusted domain, if an application on the endpoint tries to connect to an unauthorized domain, Nucleon EDR intervenes and prevents the action from exiting the device.
This supplementary approach is vital in today's landscape, since endpoints are frequently situated outside conventional network perimeters, such as on home networks or public Wi-Fi. In a cloud-native environment, for example, a program reaching out to an external server might bypass network-level scans, but Nucleon EDR evaluates whether the behavior complies with endpoint policies, including blocking access to certain whitelisted domains. This multi-layered defense establishes a robust security stance, merging network-level filtering with endpoint-specific measures. Nucleon EDR integrates seamlessly with your current network security framework, continuously providing protection without the need for complex reconfigurations and utilizing a unified defense strategy throughout your organization.
Endpoint Enforcement Layer
The Endpoint Enforcement Layer serves as the core of Nucleon EDR's Zero Trust framework, continuously applying and evaluating rules and policies.
This layer consistently monitors objects such as processes, commands, or executables and checks their actions against established policies in real-time. When a system object demonstrates unauthorized behavior, such as a process trying to alter a system file, the enforcement layer can detect the issue, halt or isolate the activity, and generate an alert for future review.
Continuous monitoring is essential in dynamic settings where threats arise from various origins, including compromised applications, stolen credentials, or insecure networks in remote work or cloud environments. For example, if a PowerShell command tries to execute an unauthorized modification, the enforcement layer enforces the appropriate policy to block the action, irrespective of the user's credentials or network location. The system provides tailored responses, including containing a high-risk process to prevent further escalation or auditing low-risk activities for later analysis, ensuring that responses are fitting to the level of threat. Nucleon EDR aims to enforce this compliance with accuracy and consistency, safeguarding endpoints effectively without hindering user productivity.
Conclusion
Nucleon EDR’s Zero Trust Rules combine adaptive learning, AI-driven protection, and endpoint-centric enforcement to deliver security that’s proactive and transparent. By understanding your unique environment through the Absorption Phase, leveraging real-time AI to catch evolving threats, and integrating with Zero Trust architecture, our solution keeps your endpoints secure without disrupting your work.
Cet article a-t-il été utile ?
C'est super !
Merci pour votre commentaire
Désolé ! Nous n'avons pas pu vous être utile
Merci pour votre commentaire
Commentaires envoyés
Nous apprécions vos efforts et nous allons corriger l'article
